Secure Data Destruction for RAM & Servers
In an era where data breaches cost organizations millions of dollars and regulatory expectations have never been stricter, secure RAM data destruction and secure handling of server hardware are essential components of modern IT security practices. IT asset managers and security officers in the United States must ensure that memory and server hardware are decommissioned in ways that protect sensitive information, meet compliance standards, and mitigate legal or reputational risk.
According to industry research, the average cost of a data breach exceeds $4.88 million per incident, underscoring how costly an unprotected endpoint can be if data destruction is neglected. For organizations needing professional support, RAM Exchange offers secure IT Asset Disposition services that integrate data protection with responsible hardware decommissioning.
This detailed guide explains how to perform secure RAM data destruction, the importance of memory data wiping, compliance requirements, and trusted approaches for handling servers and memory modules at end of life.
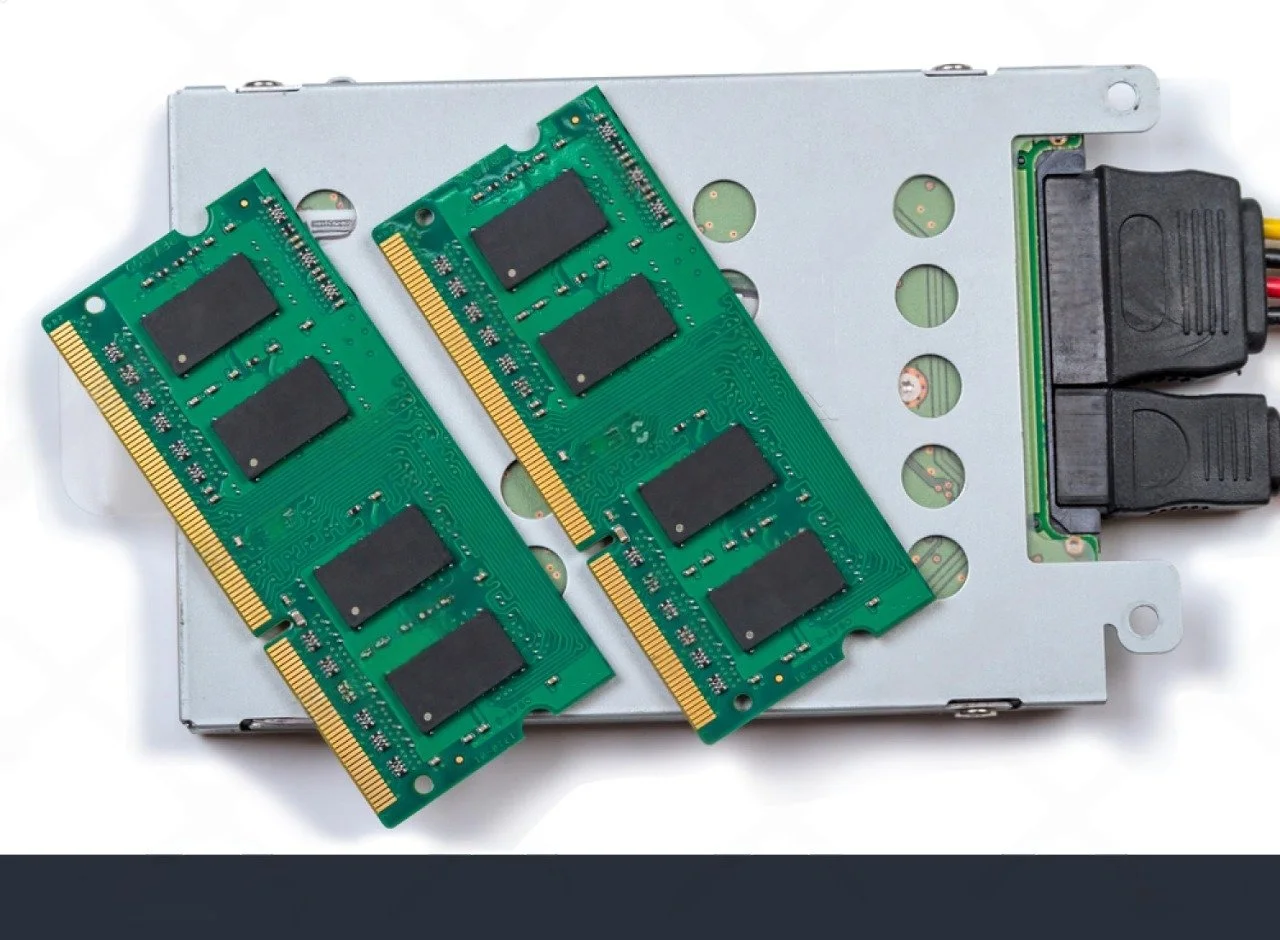
What Secure RAM Data Destruction Really Means
Strictly speaking, RAM is volatile memory that does not retain user data once power is removed. NIST’s media sanitization guidance focuses on storage media, but it still requires organizations to identify all media that may contain sensitive representations of data across the system lifecycle.
For security officers, secure RAM data destruction therefore means:
Ensuring that any persistent data associated with servers and memory (on disks, SSDs, NVRAM, controllers) is sanitized in line with NIST SP 800‑88.
Handling RAM modules within a controlled IT asset disposition program so components cannot simply “walk out the door” without documentation or due diligence.
Applying chain of custody, access controls, and certified ITAD processes to entire servers, including DRAM, to prevent any uncontrolled transfer of systems that might still hold sensitive data elsewhere.
In practice, RAM sits inside a broader ecosystem where servers, storage, and embedded controllers are sanitized, validated, and either reused or destroyed under policy.
Why Secure Data Destruction Matters
When servers and memory are retired, residual data can still exist in volatile memory caches, logs, or system states that are not captured in traditional storage drives. Although RAM itself loses data when powered off, the overall server and adjacent components often contain sensitive system metadata, configurations, cached credentials, or artifacts that relate to your business. Mistakes in decommissioning can open doors to:
Data breaches exposing corporate, customer, or partner information.
Regulatory violations with associated fines.
Audit failures due to lack of proof of secure destruction.
Reputational damage and erosion of stakeholder trust.
Furthermore, estimates suggest that North America accounted for about 42% of the secure data destruction market share in 2023, reflecting increasing demand for certified IT asset disposal services.
NIST SP 800‑88: The Foundation for Media Sanitization
NIST SP 800‑88 (Revisions 1 and 2) is the main reference security teams use when defining media sanitization and data destruction standards.
Key concepts:
Three sanitization categories
Clear: Logical techniques like overwriting that protect against simple non invasive data recovery.
Purge: More robust techniques (for example, cryptographic erase, firmware secure erase, degaussing where appropriate) that defend against laboratory grade attacks.
Destroy: Physical destruction to render media unusable, including shredding, pulverizing, melting, or incineration.
Risk based approach
NIST emphasizes that the chosen method must be commensurate with the confidentiality level of the data and the potential for future exposure.
Programmatic controls
Revision 2 highlights the need for policy, roles, verification, documentation, and continuous oversight as part of a media sanitization program.
For RAM and servers, this means that disks, SSDs, and other non volatile components must undergo Clear, Purge, or Destroy, while the handling of volatile components like DRAM must still follow secure process, tracking, and chain of custody.
Certified ITAD and R2v3: Why They Matter for Servers and Memory
Certified IT asset disposition providers operate under frameworks such as R2v3, e‑Stewards, and ISO 14001 that define how retired IT equipment is handled from both data security and environmental perspectives.
R2v3 certified ITAD providers are required to:
Implement strict data security protocols, including documented data sanitization processes tailored to various device types and risk levels.
Maintain comprehensive documentation and reporting, including detailed chain of custody and downstream due diligence from receipt through final disposition.
Ensure secure destruction workflows and controlled processing environments for media that must be destroyed rather than reused.
For security officers, partnering with a certified ITAD provider reduces the risk that servers or memory components will be mishandled, lost, or processed by unvetted downstream vendors.
RAM Exchange aligns its memory focused ITAD services with these principles by combining DRAM specialization with structured, documented lifecycle handling.
Core Methods of Secure Data Destruction
There are multiple methods used to make sure sensitive data is permanently unrecoverable. The right choice depends on the sensitivity of information and compliance requirements:
1. Logical Data Wiping
Also known as memory data wiping, this method uses enterprise-grade software to overwrite existing data patterns, making original data irrecoverable. When done to compliance standards like NIST SP 800-88, it meets many regulatory requirements.
2. Degaussing
For magnetic storage components adjacent to server memory systems, degaussing uses magnetic fields to scramble data. While not directly applicable to RAM, it is relevant to array controllers, caches, and traditional drives associated with servers.
3. Physical Destruction
For media that cannot be wiped, physical destruction is the most reliable method. Shredding, crushing, or pulverizing hardware renders storage components unusable and data unrecoverable.
4. On-Site Certified Destruction
For maximum control and compliance audit readiness, on-site secure data destruction allows your team to witness processes and verify chain-of-custody documentation, enhancing accountability.
The Secure Data Destruction Workflow
Security officers should ensure that every device going through the decommissioning process follows a structured, documented workflow.
Typical Secure Data Destruction Steps
| Phase | Objective | Controls |
|---|---|---|
| Inventory & Cataloging | Identify assets with potential data | Serial logging, tagging |
| Pre-Sanitization Audit | Determine destruction method | Risk classification |
| Sanitization or Destruction | Apply wipe, degauss, or shred | Method-specific verification |
| Certification & Documentation | Record destruction evidence | Certificates, serial logs |
| Compliance Reporting | Support audit & compliance reviews | Signed reports |
Each step should be traceable and auditable, ensuring that your secure RAM data destruction practices are defensible under regulatory scrutiny.
Components and Appropriate Sanitization Focus
| Component | Data risk focus | Typical sanitization method(s) |
|---|---|---|
| HDD / SSD | High (persistent data) | Clear or Purge (overwrite, secure erase), or Destroy. |
| RAID / SAN controllers | Medium to high (cache, config) | Clear configs, firmware reset, or Destroy if high risk. |
| RAM (DRAM modules) | Low (volatile) | Controlled handling and reuse under ITAD; Destroy only if policy requires. |
| NVRAM / TPM modules | High (keys, credentials) | Purge via cryptographic erase or Destroy. |
The key insight is that RAM’s main risk is not residual data, but uncontrolled release of intact servers or memory modules outside an ITAD framework.
Chain of Custody: The Non Negotiable Control
A chain of custody is the backbone of secure IT asset disposition.
What it includes
Detailed records of asset handoffs, including dates, personnel, locations, and conditions from initial collection through final processing.
Documentation of any changes in custody, such as transfer from your data center to an ITAD facility and onward to recyclers.
Why it matters
Proves that sensitive hardware was never left unattended or in the hands of unvetted parties.
Supports incident investigations if any anomalies arise and is often required by auditors and regulators.
R2v3 certified ITAD providers must maintain strict chain of custody controls and downstream tracking for all electronic materials. Security officers should make this a baseline requirement in any ITAD and server decommissioning contract.
Where Secure RAM Reuse Fits: Risk vs ROI
Not all RAM must be destroyed. In fact, responsible reuse through certified ITAD can reduce environmental impact and recover value.
NIST encourages reuse where appropriate: NIST SP 800‑88’s Clear and Purge categories are designed to allow media reuse when risk is acceptable and sanitization is validated.
Certified ITAD enables safe remarketing: R2v3 and similar frameworks require that any reuse is accompanied by documented sanitization and controlled downstream channels.
Financial and environmental benefits: Reusable RAM and servers can be resold as tested components, subsidizing decommissioning costs and supporting circular economy goals.
RAM Exchange operates in this reuse space for memory hardware, purchasing reusable DRAM from enterprises under ITAD aligned processes and remarketing it only after testing and certification.
How RAM Exchange Can Support Secure Data Destruction
Security officers and IT asset managers should consider a partner that understands both memory assets and secure destruction workflows. RAM Exchange offers services that integrate:
Asset evaluation and testing prior to destruction
Secure memory and server handling
Compliance documentation suitable for audit demands
Options for remarketing data devices where appropriate
End-to-end secure logistics and certified disposal
By combining deep enterprise experience with secure data handling protocols, RAM Exchange helps organizations confidently navigate their secure RAM data destruction and server decommissioning needs.
Secure Destruction Is an Ongoing Process, Not a One Time Event
Secure RAM data destruction and safe server decommissioning are non-negotiable components of modern IT security and risk mitigation strategies. By aligning processes with recognized standards, maintaining audit-ready documentation, and partnering with certified professionals, security officers can protect their organizations from data breaches, compliance violations, and financial liabilities.
RAM Exchange helps teams manage secure IT asset disposition workflows that integrate security, compliance, and responsible hardware handling. To explore secure data destruction options or discuss your organization’s specific requirements, connect with our experts.
Secure data destruction is more than a technical requirement - it is a strategic commitment to protecting your organization’s most valuable asset: its data.
FAQs
1. What is secure RAM data destruction?
Secure RAM data destruction refers to processes that ensure any memory or server component that may contain sensitive information is sanitized or destroyed using certified, compliant methods, preventing data recovery once devices leave organizational control.
2. Do RAM modules need data destruction?
While RAM is volatile and loses data when powered off, the server environment and surrounding hardware may contain residual sensitive information. Secure processes ensure no data artifacts remain accessible.
3. What compliance standards should secure destruction follow?
Standards like NIST SP 800-88, HIPAA, PCI DSS, and applicable state regulations guide secure data wiping and destruction. Certified processes provide defensible documentation for audits.
4. What documentation should I collect?
Collect certificates of data destruction, serial-level logs, chain-of-custody records, method details, and dates/times to support internal audits and regulatory reviews.
5. Can wiped devices be reused?
Yes. Devices that undergo certified logical data wiping can be reused or redeployed if data is irrecoverably sanitized according to compliance standards.
6. How do ITAD providers secure hardware transport?
Reputable ITAD partners use secure logistics, tracking, insurance, sealed containers, and documented handoffs to protect hardware and maintain accountability throughout transport.